Management Portal
Dashboard
The Dashboard provides real-time visibility into uploaded file status. Files are tracked through their lifecycle states:
- Pending: File received, awaiting transfer to destination
- Transferred: Successfully delivered to the configured destination
- Failed: Transfer failed (destination unreachable, auth error, etc.)
- Deleted: Soft-deleted from the system
Features include:
- Full-text search across filenames and metadata
- Filter by state, date range, and destination
- Paginated view (configurable page size)
- SHA-256 hash display for file integrity verification
- Click-to-copy hash values for audit trails
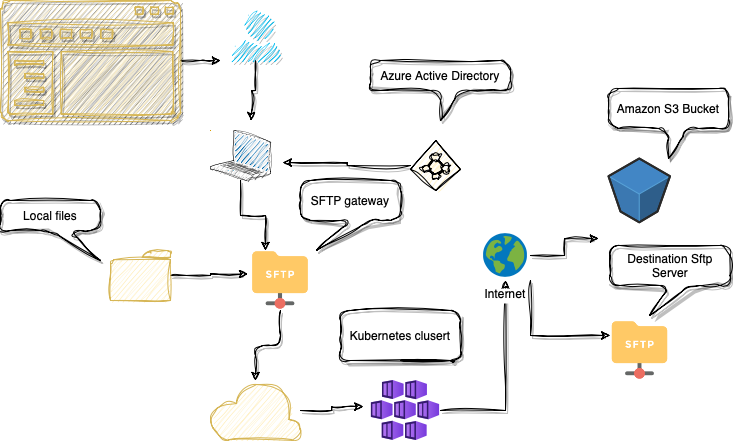
SFTP Gateway Deployments
Deploy managed SFTP Gateway instances that accept file uploads and route them to configured destinations. The deployment list shows instance status, health, and version.
Deployment states:
- Active: Running and accepting connections
- Provisioning: Deployment in progress
- Failed: Deployment error (check logs)
- Deleted: Soft-deleted (retained for audit)
Configuration parameters:
- Instance Name: Unique identifier (DNS-safe, lowercase)
- Version: Gateway version (use latest recommended)
- External Port: SSH listening port (22, 80, 8080, or custom)
- Public Port: Externally accessible port mapping
- Authentication: Username/password and/or SSH public keys
- Destination: Target for uploaded files (SFTP, S3, or Azure Blob)
Health monitoring includes connection status, last activity timestamp, and resource utilization. Deployments can be updated (version, credentials) or deleted via the UI.
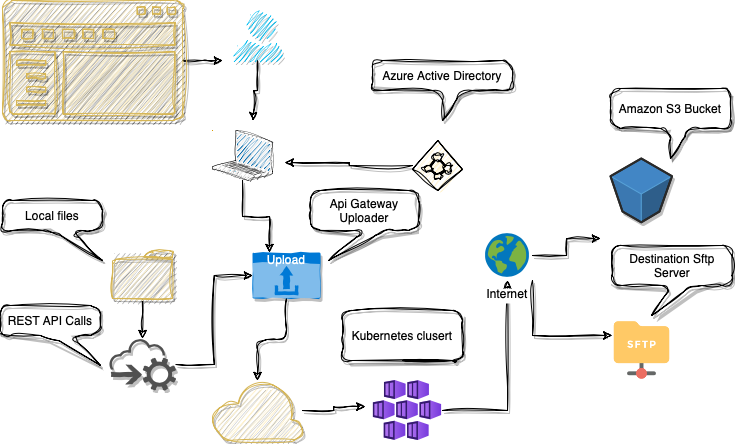
API Gateway Uploader Deployments
Deploy HTTP-based API endpoints for file uploads. The API Gateway provides RESTful endpoints for programmatic file transfer, suitable for application integrations.
Configuration parameters:
- Instance Name: Unique identifier (URL-safe)
- Destination: Target storage (SFTP, S3, or Azure Blob)
API Gateway features:
- HTTPS endpoints with TLS 1.2/1.3
- JWT token authentication
- Multipart/form-data and binary uploads
- Chunked transfer encoding for large files
- Automatic retry with exponential backoff
Use cases include application-to-application file transfer, batch upload jobs, and integration with systems that cannot use SFTP protocol.
Destinations
The Destinations page allows users to configure upload targets. The system supports three destination types:
SFTP Destination
- Alias: Unique identifier for the destination
- Hostname: SFTP server hostname or IP address
- Port: SSH port (default: 22)
- Username: SSH/SFTP username
- Authentication: Password or SSH private key
- Remote Path: Target directory on the remote server
AWS S3 Destination
- Alias: Unique identifier for the destination
- Bucket Name: S3 bucket name
- Region: AWS region (e.g.,
eu-west-1,us-east-1) - Access Key ID: AWS IAM access key
- Secret Access Key: AWS IAM secret key
- Prefix: Optional S3 key prefix (folder path)
Azure Blob Storage Destination
- Alias: Unique identifier for the destination
- Storage Account Name: Azure storage account
- Container: Blob container name
- Primary/Secondary Key: Storage account access keys
Destinations are validated on creation. Credentials are stored encrypted and masked in the UI (first 5 and last 5 characters visible).
Keys
The Keys page manages SSH public keys for SFTP Gateway authentication. These keys enable passwordless authentication to deployed gateways.
Key parameters:
- Alias: Unique identifier for the key
- Public Key: OpenSSH format public key
Supported key types:
ssh-rsa(RSA, 2048-bit minimum, 4096-bit recommended)ssh-ed25519(Ed25519, recommended for new keys)ecdsa-sha2-nistp256/384/521(ECDSA)
Generate a new key pair:
ssh-keygen -t ed25519 -C "[email protected]"
cat ~/.ssh/id_ed25519.pub | pbcopy # macOS
cat ~/.ssh/id_ed25519.pub | xclip # LinuxKeys are associated with SFTP Gateway deployments and can be reused across multiple deployments within the same domain.
API
The Public API provides REST endpoints for CI/CD integration. Authentication uses JWT tokens.
Available API operations:
- Deployments: Create, list, update, and delete SFTP/API Gateway instances
- Destinations: Manage upload targets (SFTP, S3, Azure Blob)
- Keys: Register and manage SSH public keys
- Blobs: Query file status and metadata
- Connectors: Configure notification webhooks
Integration examples:
- Jenkins pipelines for automated deployment provisioning
- Azure DevOps pipelines for infrastructure-as-code workflows
- Terraform providers for declarative configuration
- Custom scripts for batch operations
Long-running operations (create, delete) return task IDs for polling-based status checks.
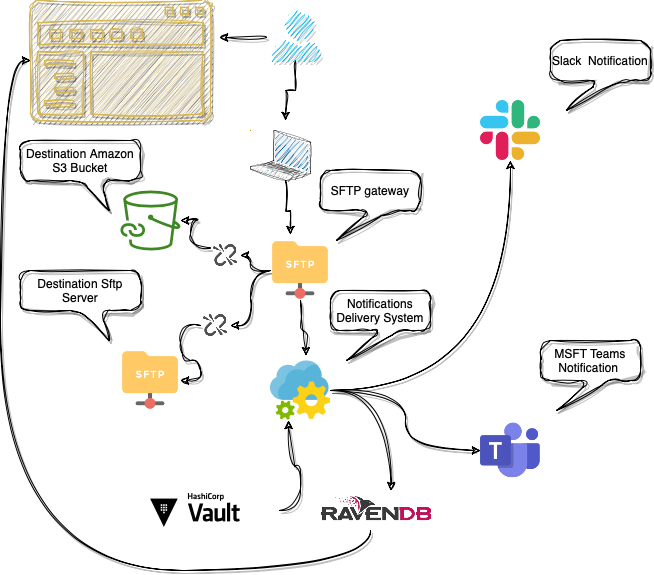
Connectors
Connectors enable webhook-based notifications for transfer events. Configure integrations with collaboration platforms:
- Microsoft Teams: Incoming Webhook URL
- Slack: Incoming Webhook URL
- Custom Webhook: Any HTTP endpoint accepting POST requests
Configuration parameters:
- Alias: Connector name for identification
- Webhook URL: HTTPS endpoint URL (validated on creation)
- Enabled: Toggle connector on/off without deletion
Notifications are sent for failed transfers, including error details and file metadata.
Notifications
The Notifications page provides a paginated event log of system notifications. Each notification includes:
- Timestamp (ISO 8601 format)
- Event type and severity
- Affected file or deployment
- Error details and suggested resolution
Notifications can be dismissed individually or in bulk. Historical notifications are retained for audit purposes.
Statistics
The Statistics dashboard provides analytics on file transfers and storage usage:
- Storage Trends: Monthly/yearly storage consumption charts
- Transfer States: Pie/donut chart of file states (pending, transferred, failed)
- File Type Distribution: Breakdown by file extension/MIME type
- Transfer Volume: Line chart of daily/weekly transfer counts
- Success Rate: Percentage of successful vs. failed transfers
Charts are filterable by date range and destination. Data can be exported for reporting.
Users
User Management is available to group owners (administrators). The portal uses Azure AD (Microsoft Entra ID) for authentication with domain-based multi-tenancy.
User roles:
- Group Owner: Full admin access (Users, Subscriptions, all deployments)
- Member: Can create deployments, destinations, and keys within the domain
To invite a new user:
- Username: Azure AD login name
- Email: Must match Azure AD email (validated)
- First/Last Name: For display purposes
- Job Title: Organizational role
User seats are limited by subscription tier. Invited users receive Azure AD-based access and inherit the domain's resource quotas.
Subscriptions
Subscription management is available to group owners. Billing is handled via Stripe.
Subscription tiers control:
- Number of SFTP Gateway deployments
- Number of API Gateway instances
- User seats (team members)
- Storage quotas and transfer limits
Subscription page features:
- Current plan details and usage metrics
- Upgrade/downgrade options
- Billing address and VAT number management
- Invoice history and receipt downloads
- Payment method management (via Stripe portal)
Session Security
The portal implements JWT-based sessions with the following security measures:
- Session Timeout: 8 hours of inactivity
- Token Refresh: Activity-based refresh every hour
- Immediate Logout: Token blacklisting via NATS for instant session invalidation
- Audit Logging: All authentication events logged (login, logout, failures)
SFTP Gateway Diagram
API Gateway Uploader Diagram
Scenario:
Local-to-External Vendor Document Transfer via SFTP Gateway
Alex works as an IT administrator in a manufacturing company that deals with sensitive document transfers on a regular basis. Recently, the company has partnered with an external vendor who requires them to securely transfer various documents.
To facilitate this transfer, Alex decides to leverage the Almeria Industries SFTP Gateway system within their organization.
Here's how he proceeds:
Configuration:
Alex accesses the Almeria Industries user interface and navigates to the "SFTP Gateway" section. He creates a new SFTP Gateway configuration, specifying the necessary parameters such as hostname, port, and authentication method. Additionally, Alex sets up the required security measures, including encrypting the files, to ensure secure document transfers.
Document Transfer:
Alex locates the documents in the local directory that need to be transferred to the external vendor. He initiates the document transfer process through the local SFTP client that will be connecting to the SFTP Gateway. The SFTP Gateway system establishes a secure channel with the external vendor's SFTP server. Using the established connection, the documents are securely transferred from the local directory to the external vendor's server, ensuring confidentiality and integrity throughout the process.
Notifications:
Alex wants to stay informed when data transfers encounter issues at the destination due to network connectivity or incorrect credentials. To make sure he is always notified, he sets up a new Connector. This Connector acts as a bridge and links up with his chosen channel on Microsoft Teams, using an incoming webhook.
Contact
Location:
Almeria Industries
Bucuresti, Calea Moșilor Nr. 88, Sector 3, 020851
Romania